
Moving from spying to sabotaging autonomous industrial systems STUXNET was designed specifically to utilize vulnerabilities in the Microsoft windows to target Siemens Software and Equipment running a Uranium Enrichment Facility in Iran.
60% of STUXNET effected computers were inside Iran which showed to the world how malware can be used to target specific geographic locations.
STUXNET was designed to target SIEMENS software and Equipment, the designers of the software knew what hardware and software the malware would be looking to destroy. The malware STUXNET was able to inflict a sizeable blow to the nuclear program of Iran, sizeable enough that Iran publically had to admit that its systems had been hit.
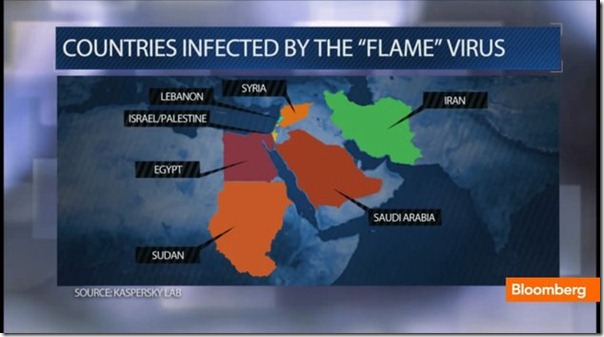
Kaspersky Lab has recently claimed responsibility for discovering an even more comprehensive Malware which has been named “FLAME, Skywiper, and Flamer.A”, a discovery Kapersky made while it was investigating reports of a virus affecting Iranian Oil Ministry computers.
Experts at Kaspersky Lab claim that FLAME has a lot of resemblance with STUXNET and they deploy the same method of spreading which is generally by infecting and utilizing USB’s and Local Networks; in fact it is highly likely that it was developed by the same team which developed STUXNET and is being utilized by the same country that launched STUXNET.
Iran’s National Computer Emergency Response Team said that FLAME might be linked to recent cyber attacks that were responsible for massive data losses on some Iranian computer systems.
Although FLAME has resemblance with STUXNET but experts are saying that FLAME is more advanced form of STUXNET. The FLAME virus contains 20 times more code than STUXNET. FLAME can remotely gather data files from your computer, can help the host remotely change settings on an effected computer, turn on PC microphones to log or record conversations, take screen shots and log instant messaging chats. The virus can even log activity on the computers Bluetooth device.
The malware currently is built around 20 different modules most of which analysts do not even know what they might be used for and are nominating FLAME as the world’s most complete & comprehensive cyber spying toolkit to date.
Experts at Kaspersky lab are estimating that FLAME has been operational for the last 5 to 8 years which points towards this very scary question that if this was the capability of the malware 5 years ago what an advanced version of FLAME would be capable of today. The creators and controllers of the virus utilized a network of more than 80 servers across the globe to remotely access infected machines.
Uncovering of FLAME clearly indicates that National Security and security of commercial, industrial and even nuclear assets might not be as safe as we think. In reality cyber warfare has added a whole new dimension to this scenario, clearly showing the world how technologically advanced countries can utilize their knowledge superiority to attack other countries using methods or platforms where legal jurisdiction is loose.
In simpler words dismantling a countries nuclear program by utilizing FLAME or STUXNET would be more feasible in comparison to taking out a countries nuclear program with a full scale military strike. The political, economical and social implication of doing the latter is greater, carries more consequences and has far more repercussion.
Pakistani Cyber users need to be aware of this ever evolving threat, although Flame was reported to have been targeting Middle Eastern countries it is highly likely that computers in Pakistan might also be infected.
There is also high possibility that this Malware might have already infected our military and industrial networks because we do not have any mechanisms, labs to asses these kinds of threats.
Pakistan being the only Muslim Nuclear power in the world makes it an even more inviting target for such attacks therefore it is the need of time that authorities and individuals in Pakistan start considering this form of warfare as a threat and respond to it in an appropriate manner.























Aor promote karo M$ Windoze ko.
HEC higer-ups ought to be tried for criminal negligence, better yet, for treason for making deals with M$ in creating M$ Zombies in the universities & ultimately the country.
Abb to baaz aa joo sirf zardari naheen hai, yai tumhari bi ghaltiyan (blunders) hain.
Thanks For Update On Cyber Security Issue :)
Why do i feel that this blog is starting to get political rather then technical day by day?
I think its time for me to switch to some other site that would be interested in news not the politics
@ Anas Saleem
Where is the politics in this post, i cannot see it? Relevant examples have been provided where governments/administrations that were actually prepared for such a threat actually failed.
Why are people so adamant on keeping their eyes shut towards a threat that has already evolved into a potential game changer.
We must defend and response to this threat
This is indeed a serious threat. Pentagon even went to levels to formulate a formal strategy and presume ‘Cyber Attack’ equal to an actual act of War.
This is a very interesting report to follow on this topic: http://www.nytimes.com/2011/06/01/us/politics/01cyber.html
And of course, Pakistan is also vulnerable for future attacks.
And on a relative note, it make sense now as why China never used their American software
— And on a relative note, it make sense now as why China never used their American software
Total BS. They DO.
See also http://www.neowin.net/news/ballmer-9-out-of-10-copies-of-windows-in-china-is-pirated
US ordered the STUXNET Cyber attack against Iran.
http://www.theverge.com/2012/6/1/3056505/us-cyberattack-stuxnet-iran-nyt-investigation
New era just begin.This malware very interesting program for security analyzers but very dangerous for governments.
These malwares move world to very worst situation.
1.STUXNET
2.DUQU
3.Wiper/Viper (could be module of Flame)
4.Flame
Confirmed by Russia Today news: US unleashed Stuxnet cyber war on Iran to appease Israel
http://j.mp/JAMfg
If above link is broken
http://www.rt.com/news/iran-us-israel-cyberwar-virus-weapon-770/
yar yahan roman urdu mai bh btao ye hai kia chiz subha se bechain hon pata nai kia hogaya hai. plz admin aap roman urdu mai btado iski detail stuxnet konsa bhoot hai. sab ko english nahi aati.
I could develop the virus exactly as FLAME,
which remotely steals and gather data from the victims pc, I’ll have a choice and full control to whatever i want to do inside victim’s computer. like taking screenshots, stealing photos, stealing documents of my own choice or even create my own user acccount inside his PC.
Not sure about spying through microphone i.e enabling the microphone but i’m pretty sure i can do this with some extra efforts, but doing all these require time and energy and unfortunately i don’t have much time to develop a virus with all these capabilities but pretty soon i’ll come up with the demo on how FLAME/STUXNEXT could possibly managing and stealing all such data.
Stuxnet is a delivery vehicle for a virus that targets specialized microcontroller type chips in industrial computers, not windows systems. Can your virus target them, too??? No x86 experience will help here…
I feel every country should have its Own Base OS, or you can say a customized Secured *nix Versions.
u sort of nailed it !
Is Israel behind the ‘Flame’ worm?
Security researchers are warning of what they call one of the most sophisticated worms to date, and believe that this time, the worm may be the work of a nation-state rather than hackers. Called “Flame”, the Trojan has hit Middle Eastern countries particularly hard, most notably Iran.
According to Kaspersky, Flame is capable of stealing “computer display contents, information about targeted systems, stored files, contact data and even audio conversations”. The worm appears to be targeted to specific computers, likely indicating its creators are searching for specific information.
Unique to Flame is its usage of Bluetooth. In theory, any Bluetooth-enabled device nearby could also be at risk, as the worm also attempts to collect data via file transfer from those mobile devices.
“One of the most alarming facts is that the Flame cyber-attack campaign is currently in its active phase, and its operator is consistently surveilling infected systems, collecting information and targeting new systems to accomplish its unknown goals”, Kaspersky Lab chief security expert Alexander Gostev says.
Flame is quite large in size — about 20 megabytes. This would make it over 20 times the size of the Stuxnet worm.
Given that Flame appears to be targeting Middle Eastern governments, suspicion that this may be the work of hackers connected to the Israeli government is high. While the Jewish state has not taken responsibility for the attack, the comments of Vice Premier Moshe Yaalon did little to quell speculation otherwise.
“Whoever sees the Iranian threat as a significant threat is likely to take various steps, including these, to hobble it”, Yaalon is reported to have said on Israeli Army Radio Tursday. “Israel is blessed with high technology, and we boast tools that open all sorts of opportunities for us”.
Even with Yaalon’s comments, it is still important to note that Kaspersky found Flame on computers in Israel as well, although nearly every other country that Flame has been detected in — Egypt, Iran, Lebanon, the Palestinian Territories, Syria, and Sudan — do not have the best relations with Israel.
Flame evaded detection for two years as it was successfully able to morph itself by attempting to detect what antivirus software was running. From there, it would hide itself in files that the antivirus software would not expect to be holding malicious code.
That is the biggest problem here, say experts. Traditional antivirus techniques failed, and Flame is successfully exploiting these holes.
“The reality here is that threats, regardless of whether they are crafted by nation states or not, find their way into networks”, SourceFire development chief Alfred Huger said of the news. “Most technology focuses on stopping threats yet gives us little recourse if they fail to do so. This is the area that needs attention when we talk about threats like Flame. The gap that presents itself in the ‘what if’ and ‘what now’ is best summarized by a lack of visibility and a lack of control”.
The solution is simple why do you want access the most sensitive data through internet just put it offline.
You must be the king of not paying attention. Stuxnet was actually installed using a flash, not over the internet. The facility that was targeted was already off the internet.