A hacker or hacking group has claimed they have carried out a cyber attack on another group related to the National Security Agency (NSA). The hacker(s), who are going by the name “Shadow Broker” have shared some of the hacking tools they used in the attempt.
To make matters more serious, the Shadow Broker is asking for 1 million in Bitcoins (around $567 million) in an auction. They are threatening to release the files they’ve successfully collected to whomever pays the ransom.
The hackers wrote in a manifesto:
How much you pay for enemies cyber weapons? We find cyber weapons made by creators of stuxnet, duqu, flame. We find many many Equation Group cyber weapons. We give you some Equation Group files free, you see. But not all, we are auction the best files.
The cyberattack group hacked by Shadow Broker is called Equation Group which is a codename for a government hacking group believed to be part of the NSA.
Equation Group’s Background
Kaspersky Lab, the online security firm, mentioned the Equation Group back in 2015 as the most advanced hacking group they’ve ever seen.
They also provided evidence which pointed to the Equation Group being related to the NSA but never outright said it.
The Equation Group (according to Kaspersky Labs) targeted the same victims as the ones targeted by the group behind Stuxnet (US-Israeli joint operation against Iran’s nuclear facilities). They also used two zero day exploits which also matched the ones used by NSA.
About the Sample Files
Shadow Brokers claim that they hacked the Equation Group. As a preview, they shared some of the hacked files for public viewing, sending them to various media companies as proof of its exploits.
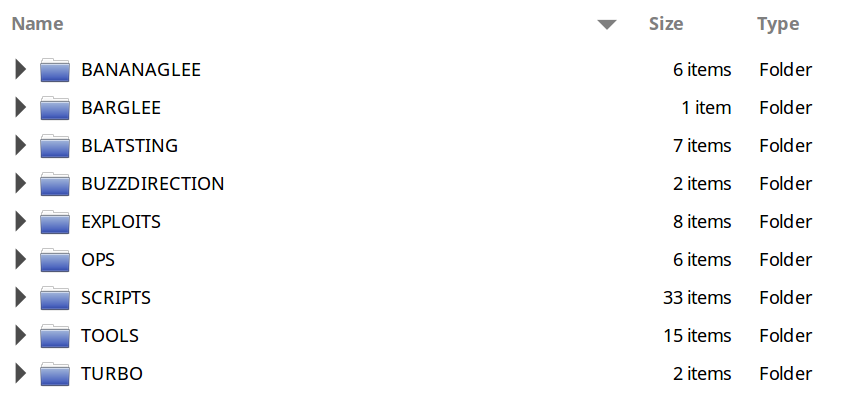
Some of the names of the files sent to the media are similar to those released by Edward Snowden. They contain similar terms such as “BANANAGLEE” or “EPICBANANA” for example.
Details are sketchy about the nature of the hack used by the Shadow Broker. The group states that they did so by following the Equation Group’s traffic, hacking them and taking their “cyber weapons,” referring to the tools that the NSA uses to spy for its own purposes.
Real or Not?
The files themselves pose a question of legitimacy. Are they the ones which actually belong to Equation Group or not? Are they high-profile or just low-key?
Those questions are going around in hacker circles right now. Many have chimed in with their thoughts about the whole episode.
A researcher by the name of “PWN All The Things” says,
I think it’s hard to say at this stage whether the files are genuine, but they are an elaborate hoax if not, by someone who has spent a lot of time going through the Snowden documents to sprinkle codenames into the files.
Another security researcher by the name of “The Grumq” holds another view:
The proof files look pretty legit, and they are exactly the sorts of exploits you would expect a group that targets communications infrastructure to deploy and use.
A former British intelligence officer and a security researcher, Matt Tait thinks that these files could have come from “an old counter-hack”.
A Kaspersky Lab researcher thinks that these files have nothing in them which links back to the Equation Group. However some of the names are straight out of the ANT Catalog, a NSA hacking toolset published in late 2013.
Whether the hack is legitimate or just a hoax is still inconclusive at the moment. But the potential ramifications of this hack can’t be ruled out. If it is indeed a legitimate hack that has targeted NSA or its subsidiaries, this can have huge implications for both cyber security as we know it as well as the national security of America.





















Bazingaa!!
By reading their English in manifesto, I can confirm that these hackers are from China. :)
My thoughts :)
Besides that they might belong to Tamil Nado
How can you be that much sure..??? They are hackers and they certainly are smart enough to give an impression of bad English. Although you ought to research a lot more about NSA in order to blame explicitly.
Shadow Broker? Looks like someone is a fan of Mass Effect here. :D
Hackers are asking 1M bitcoins ( $576)
You mean $576M
Yes
Sorry for typo
Yeah right. A loser’s attempt at scamming gullible idiots in various agencies of wannabe countries. And stealing from apparently the best hack group? Yeah right.
It happens.
NSA is selling their old stuff?