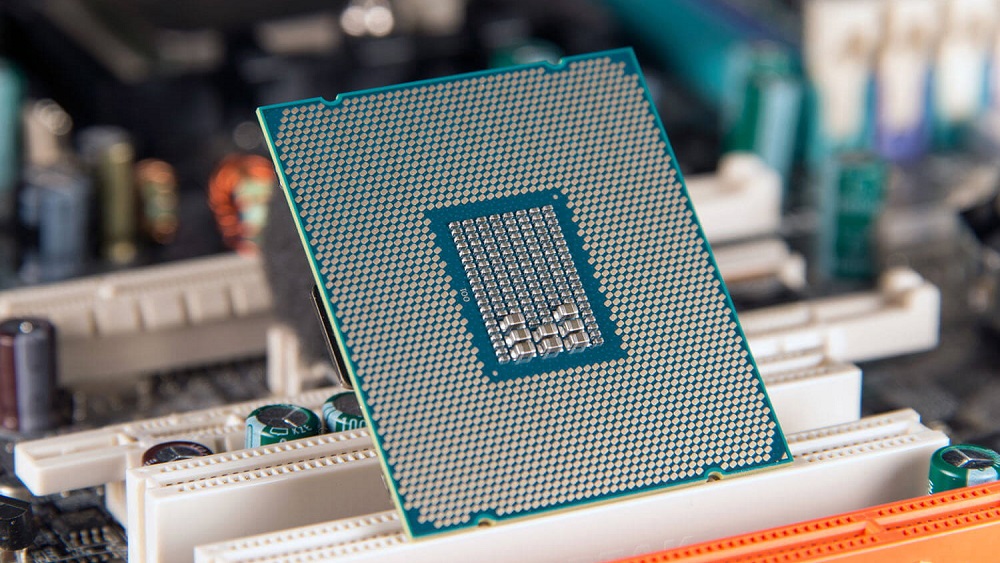
Today, Intel detailed a new set of processor vulnerabilities in their press release. They allow hackers to steal info stored on clouds and on computers.
Discovered and reported to Intel back in January this year, it comes in three different variants. The company says that most users would not be affected by these vulnerabilities, thanks to updates released earlier this year, and more updates coming out now.
ALSO READ
AMD Takes the Crown from Intel for the Fastest Chip in the World
According to Intel,
We are not aware of reports that any of these methods have been used in real-world exploits, but this further underscores the need for everyone to adhere to security best practices.
This one doesn’t have a fancy name like Meltdown or Spectre and is instead called L1 Terminal Fault or L1TF for short.
About L1TF
A video from the chip-maker details how the fixes take care of the first two variants, while the third one only affects “a subset” of users.
As mentioned in the video, the third vulnerability will require additional measures to fully mitigate.
Foreshadow
Researchers that discovered the vulnerabilities also described an attack called Foreshadow. L1TF affects something called Software Guard Extensions, which is the next potential point of attack after Spectre and Meltdown, according to the researchers.
Daniel Gelkin, one of the researchers that helped discover this problem said,
When you look at what Spectre and Meltdown did not break, SGX was one of the few things left. SGX was mostly spared by Spectre, so it was the logical next step.
You can learn more about Foreshadow and how it affects computer systems in the video below.
Click here for a full list of affected Intel processors vulnerable to L1TF.
With the increasingly negative press, Intel needs to do something fast if it wants to retain its loyal consumer base.
Via Engadget