Spyware attacks are more common than you think. In many cases, where companies cannot be targeted directly they face indirect cyber-attacks instead. Recently, in a similar situation, WhatsApp was unintentionally made part of the process.
A buffer-overflow weakness in the Facebook-owned messaging app allowed the attacker to plant Pegasus, a type of spyware, in the victim’s smartphone. This cyber-attack gave the hacker access to all encrypted chats, phone calls, microphone, contacts, photos, basically anything and everything on the phone.
WhatsApp and an Israeli software group NSO, both have confirmed the buffer-overflow bug. They have acknowledged that it is not necessary for the victim to pick up the call, just getting the notification for the call on their device is enough for the hacker to plant the virus.
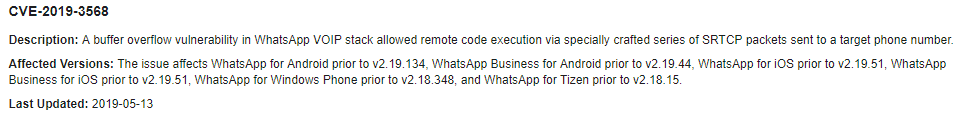
The description WhatsApp gave for the bug is shown in the following image.
Affected Targets
The virus planted in the victim’s phone belongs to NSO and is licensed to the government. It is used by the government to gain access to their targets. According to NSO, the list of victims is pretty short but still, the hackers have not been identified at the moment.
NSO and WhatsApp tracked the recent attack to the on-going human rights practices in the Middle Eastern countries. One of the failed cyber-attack attempts was made on a UK-based human rights lawyer who helped a Saudi protestor.
Human right activists in the region have previously attempted these attacks as well.
WhatsApp Update
WhatsApp was notified about the bug at the start of May and the company has issued a fix on the server side by May 10th. The secured versions of WhatsApp were sent out on 13th May, for Android and iOS versions since the buffer overflow vulnerability is found in both versions.
The official statement from the company reads,
WhatsApp encourages people to upgrade to the latest version of our app, as well as keep their mobile operating system up to date, to protect against potential targeted exploits designed to compromise information stored on mobile devices.
















How We to Know that ?
thank you for updating.
اس میں واٹس ایپ اور اسکی مالک کمپنی فیس بک کے بارے میں جو کچھ بتایا گیا ہے وہ اصل حقائق کا شائد ایک فیصد بھی نہیں۔ 2007 سے واٹس ایپ کی مالک کمپنی فیس بک خود پرزم کے ذریعئے اس طرح کی حرکتوں و معاملات کی پارٹنر ہے اور فیس بک کے واٹس ایپ کو خریدنے کے بعد سے ہی یہ سب کچھ ہو رہا ہے۔ لوگوں کو عموما” فیس بک گروپ آف کمپنیز کے بزنس ماڈل کا پتہ نہیں۔ فیس کی مالک کمپنی خود واٹس ایپ کے ذریعئے تمام صارفین کا ڈیٹا اکھٹا کرکے خفیہ طور پر فروخت کرتی ہے۔ جب کچھ کچھ عرصے میں انکے اسکینڈل سامنے آتے رہتے ہیں تو مختلف حیلے بہانے بنا کر خود کو معصوم ظاہر کرتی ہے۔
اس وقت ٹیلیگرام، وائر اور برائر کے علاوہ کوئ بھی میسنجر استعمال کیلیئے محفوظ نہیں۔ باقی جو جس کا دل چاہے سوچھے، سمجھے یا استعمال کرے اسکی مرضی۔
Telegram Viber IMO Etc Main Wo Maza Nahi Jo WhatsApp Jaise Main Hai
Ya to in 3 Apps Ko WhatsApp Jaisa Bana Lo
Brother,
These are few options of Telegram:
Unlimited Cloud encrypted Storage for your all chats,
Unlimited Channels for the best contents of any type including latest HD Movies, Dramas, Music, Softwares, etc.
Unlimited Group members,
Customization of your every contact’s notifications,
3 separate Accounts in the same Messenger for different needs of Office, Home, Business,
Call Control enabling you to Control who can Call you or only message you,
Ability to stay in touch either with Phone number or your User name,
Ability to call or message with built in proxy for maximum connectivity in countries where internet traffic is blocked.
Telegram users know how fantastic it is.
True.