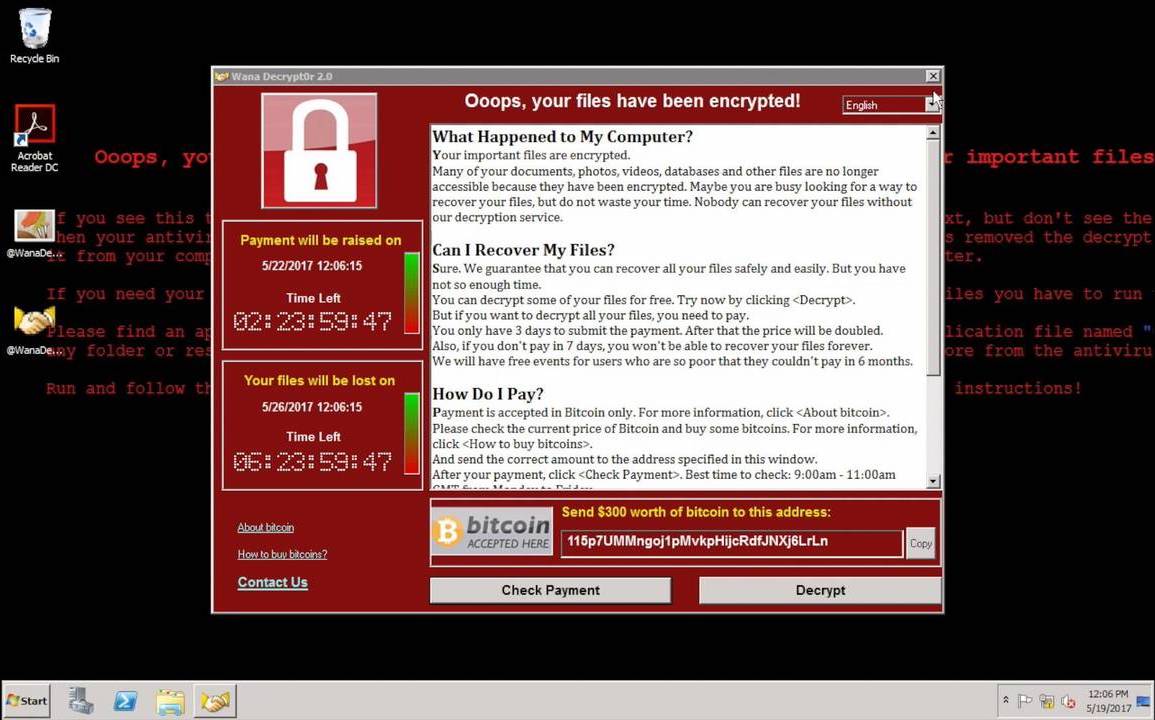
Two years ago, powerful ransomware called WannaCry spread all across the globe hitting millions of computers in 150 different countries. It used an exploit which encrypts a user’s files and demands ransom in return for recovering them.
This was later found out to be a coordinated cyber attack by a hacker group believed to be working for North Korea. The hackers relied on highly classified hacking tools (DoublePulsar and Eternal Blue) which were stolen from NSA and published online for anyone to use.
Using DoublePulsar, the hackers created a persistent backdoor to deliver the WannaCry ransomware, and using EternalBlue, the ransomware spread on every other unpatched computer on the network.
Using these exploits, WannaCry spread over the world, infecting millions of computers and causing billions of dollars in damages.
Later on, NotPetya, another ransomware which used the same NSA tools attacked shipping giants, supermarkets and advertising agencies causing even more damage to different industries across the planet.
Millions Still at Risk
Two years later these NSA tools are still at large and continue to pose a threat to millions of Internet-connected endpoints. Shodan, a search engine for exposed databases and devices puts the figure at 1.7 million with most of these devices belonging to the US.
Just a few weeks ago, the city of Atlanta was hit by ransomware on its networks caused by the same NSA tools. These tools have recently been reprogrammed to infect computers with cryptocurrency mining code to generate money or infect them with distributed denial of service (DDoS) attacks with massive amounts of internet traffic.
Though most of the said vulnerable devices are in the US, there is still a significant chance that a chunk of those exist in Pakistan as well. Users are advised to keep their systems and software up to date as most of these vulnerabilities are rapidly being patched by software and hardware companies.