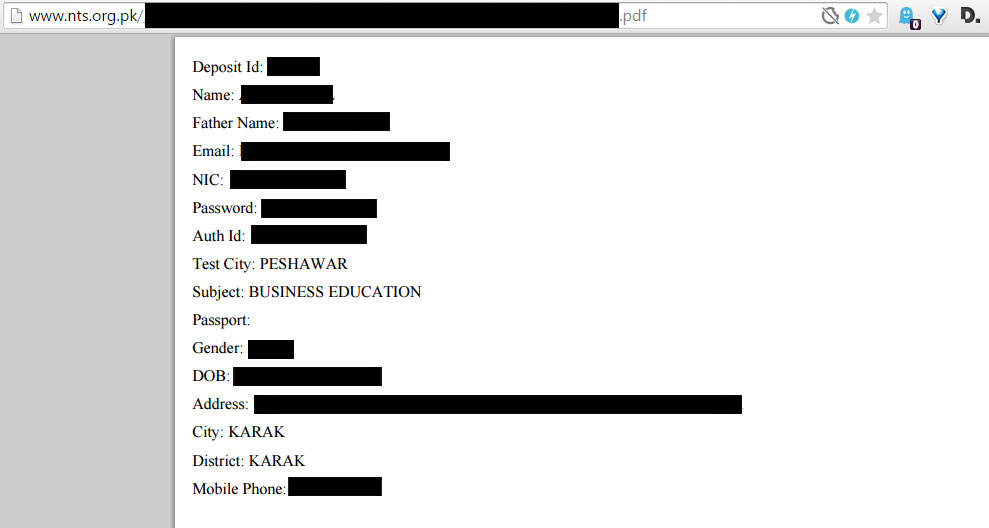
Another day, and we have another local firm that isn’t taking its privacy seriously. NTS, the leading testing service in the country, is exposing private information of each and every applicant out in the open world wide web.
This information stored on NTS servers, for several hundred thousand students, is exposed to the world that includes extremely private data including names, father name, passwords, home addresses and what not.
The information which can be accessed is as follows:
- Deposit ID
- Name
- Father Name
- NIC
- Password
- Auth ID
- Test City
- Subject
- Passport
- Gender
- Date of Birth
- Address
- City
- District
- Mobile Phone
We do not want to publicize the exact format of the URL due to the sensitive nature of the information but here’s a screenshot.
We were able to access information of hundreds of candidates and we are sure that anyone with moderate technical knowledge could quickly build a database with the available data.
Frankly, it is absolutely incredible that an organization raking in money by the bucket loads can’t even be bothered to properly secure its servers. Even if they do, there must be a better way to store information than in plain text PDFs, that are easily accessible.
Security is often not even factored into the equation in most companies. Quality assurance is one of the most critical areas for any organization that relies on the internet or computers and it’s time that fact is widely recognized in Pakistan.
We call upon NTS to give due attention to this matter and resolve this gaping security hole at once.
No wonder you will see tons of ads on this semi government website, hinting that the people running and maintaining this website are more concerned about the money and not about the look and feel and other important aspects of the website.
Thank you Ali for tipping us on this.




















Another Rasgulla for our Parha Likha Pakistan.
NTS is a pure moneymaking machine with no accountability
Although you have not published the full url here, but anyone with little knowledge about web can easily find all this data, It will take few code changes to secure this data, But I know they will still not do anything, just like many other organisation in Pakistan, no one cares to protect personal data of their users . :(
How?
Yes, i am currently downloading some 13K data records :)
How??
plz share link to
03444260270
NTS should be ban in Pakistan and shut it down its leeching money from every one with no cause
100% agree…its bulsh*t service..they just earning money i was thinking about why no one talks about NTS so called service who is just earning money nothning more…..nice to c this post..
angoor kathay hein boy
beta angoor ho gy to kathy ho gy.
You know what’s even more interesting? Most of us have just one password for all the accounts.. so i wont be surprised if the password used over there would be the same password of their email, facebook and other important accounts..
well if you have only one password for your account then its your fault :P
NTS is “Employment for Unemployed “
The Web Developer Don’t know How to Prevent a Directory Listing of Your Website.
BTW I have got the list :D
how can one get one?
How??? MSG ME!
Thanks for taking my News Tip, Cheers,
Have they responded yet?
Did you find it?
Yes,
How did you find it?
just use your mind… if you have one… acha hai tm Mand use nai kar rahy ,, kyo k tm galat use ekaro gy es lea rehny do…
It has been fixed now.
No, it is not
Fixed Now
Apko ye 14000 main mil jaye gi 03126969289
Shukar hay, NTS kabhi nae dia :D
Wow what a find! pretty easy to get the list.
And most notrious ppl must have taken it.
NTS is a subsidiary of COMSATS which claims to be the best IT university of Pakistan, to phir best IT university ne kesa diya?!
edX, udacity, coursera.
For NAB recruitment, they registered 75000 candidates on just 200 seats. Each candidate had to submit 500- Approx for the test. so total earning for NTS was 37,500,000-. The test based on mathematics , english nothing related to the post and your qualification Good job Govt. of Pakistan!
almost every university earns the same amount of money during admission process every year. do you go against all universities? do u sue them? do you stop getting admissions in those universities?
I will support any step or movement to get rid of this looting mafia called NTS.
I just found a file that has over 180,000 Records of just one Position Oh God they have it in excel all the data with cell no. to address and what not. They should be sued
cell no wali file kidr hy :/ i found with F.Names and CNICs
03215011028 link to msg kar do
can u share it with us so we can together sue them.
And they even have a ‘Privacy page’ – Everyone, please read it. It sounds amusing now.
http://nts.org.pk/privacy.php
Just visited their websites from mobile. Its full of annoying ads, popups and nothing else. Never seen this on any govt/institutional website before. The webmaster should be investigated.
NTS is “Employment from Unemployed “
NTS, should be banned and an alternative service should be offered my cousin has spend lots of money on these tests, and gets nothing, he has applied for various govt. jobs clears the test but some times doesnt come on merit or whatever. NTS is leech it is sucking money out of our people. True that NTS is “Employment for the unemployed”.
this means that theres a problem with your cousin, not with nts
and when i tried to do it they hide it fagoots
still working just need to use brain
i went to dir but couldnt find that file i uesd my brain for 2 hours on thi ssheet
They have removed it. Not accessible now.
This is totally unacceptable! A few simple steps can avoid such disaster, but they have other priorities than securing people’s data. Govt should implement data/privacy regulations and take serious action against such organizations.
Totally fake. Nothing accessed. I tried.
grapes are sour…..
It just boggles my mind of the idiocracy in Pakistan. Although the pdf(s) are not Hot-linked any more but a google webcache is still present. And we all know, female(s) details will be most people after…
site:nts _org_pk filetype:pdf deposit id
Fixed Now. I checked
still accessible via webcache
#WTF
I tired two random ids and was able to login successfully. I can’t believe this. Just imagine what those evil minds will do.
We should tell our friends who appeared in NTS to change their password immediately.
@syed_talal You should have removed the .pdf from link, kindly remove that now and delete this comment after…
All of the data is still accessible, if you can contact nts then you should definitely approach.
can any one tell how to obtain result list when it is not given on nts