Security researchers have bad news for everyone.
A new malware named ‘EternalRocks’ has been discovered which uses 7 of US’s National Security Agency’s exploits. These exploits were discovered in April, and leaked by ShadowBrokers hacker group. In other words, this new malware is ready to wreck some serious damage given its sophisticated programming.
The new malware can strike at any time, which makes it more dangerous than anything else.
Earlier, the WannaCry ransomware hit an estimated 300,000 computers worldwide. The victims included hospitals, schools and offices. WannaCry was stopped by accident, and the creators behind EternalRocks malware may have learnt from that experience.
EternalRocks was discovered by Miroslav Stampar, a cybersecurity expert from Croatia’s Computer Emergency Readiness Team (CERT) on Wednesday. Stampar says that the earliest traces of EternalRocks dates back to May 3rd.
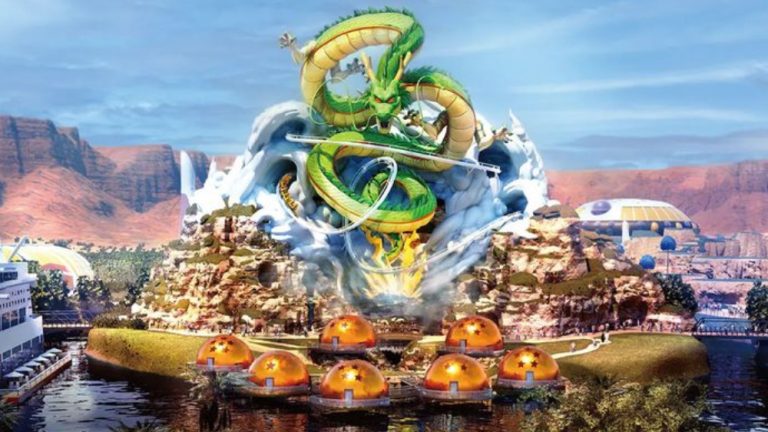
WannaCry
WannaCry used just two NSA exploits (also leaked by ShadowBrokers) called EternalBlue and DoublePulsar. Researchers also discovered another malware known as Adylkuzz which used the same exploits and created botnets for mining bitcoin and other cryptocurrency.
As for EternalRocks malware, it uses EternalBlue, DoublePulsar, EternalChampion, EternalRomance, EternalSynergy, ArchiTouch and SMBTouch exploits. All of these tools were leaked by the same ShadowBrokers group. Miroslav discovered it when it infected his honeypot (a trap to discover hidden malware).
Several PCs Still At Risk
Most of these tools use Microsoft Windows Server Message Block which is a standard filesharing tech used in PCs. Even though these vulnerabilities were patched out by Microsoft back in March, scores of un-updated computers are still at risk.
The difference between WannaCry and EternalRocks is that the latter doesn’t announce its presence when it infects your PC. After downloading on your PC undetected, it downloads Tor’s private browser and pings the worm’s hidden servers.
Uses Tor to Communicate and Replicate
For those who don’t know, Tor is a privacy-focused browser that “helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.”
In other words, it helps you go incognito.
After pinging its hidden servers, EternalRocks sits quietly inside your PC for 24 hours. After the time passes, the servers begin downloading and replicating the malware, helping spread it to other systems online.
CEO of security firm Plixer, Michael Patterson says,
By delaying the communications the bad actors are attempting to be more stealthy. The race to detect and stop all malware was lost years ago.
Hides as WannaCry
The worm even names itself as WannaCry to evade security researchers. Stampar said that unlike WannaCry, EternalRocks doesn’t have a killswitch which makes it difficult to quarantine and eliminate.
For now EternalRocks is dormant and spreading to more and more computers. It can strike at any time, similar to how WannaCry struck thousands of computers all at once. Plixer warns that the worm could be easily weaponized to act as a ransomware or a trojan.
It is hard to say how many computers have been infected with EternalRocks due to its stealthy tactics.
Right now, it is advised that you update your computers with the latest patches released by Microsoft. Hopefully that will be enough to stop the threat posed by EternalRocks malware.
Via CNet