A security backdoor is exactly what it sounds like: a secret entry point. It allows entrance into a computer program, giving the person access without having to go through the usual security mechanisms. It is usually installed by the programmers to control trouble shooting, debug and test programs. However, legitimate use of backdoors is now being contested due to risks of security exploits, hackers and even risk to privacy.
The Snowden Revelations
Edward J. Snowden is a computer analyst and former Central Intelligence Agency officer and National Security Agency contractor from U.S. He revealed how U.S intelligence agencies defeated privacy and security by showcasing the top-secret NSA (National Security Agency) documents leading to revelations about US surveillance on phone and internet communications. They cracked online encryption which protected the privacy of millions of people, compromising the guarantees of internet companies.
This revelation created an uproar which led to NSA’s invasive program being declared unlawful and disowned by the United States Congress. The UN also declared mass surveillance a human right violation. However, this doesn’t mean that security backdoors are still not exploited by governments and security agencies worldwide in the name of law enforcement. Encryption backdoors are a major issue in the privacy rights debate.
WikiLeaks – Accountability or Invasion of Privacy?
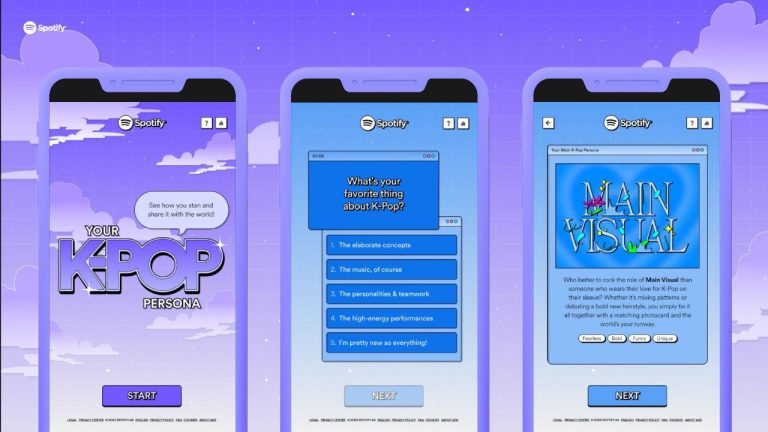
Julian Assange set up WikiLeaks, a website which published confidential documents and images. He was blamed for endangering lives by putting very sensitive information on public domains. This data could not be denied by the masses but the fact remains that he procured it through manipulation of the modern communication and more importantly, encryptions and security mechanisms.
Security Backdoors Failures
Even if security backdoors are legitimized in the same of the greater good, the fact remains that if the governments and security agencies can gain access, so can talented hackers. Then, the only party which faces the negative implications of security backdoors is the users who are unaware of their existence. There are many examples which provide evidence to prove the failure of this ‘apparent security’:
TSA’s luggage locks hacked: Hackers have created ‘master keys’ for Transportation Security Administration-recognized luggage locks which are accessible to anyone who owns a 3D printer. These locks were introduced to provide security and improved customer service. TSA is not very concerned about the fact that this will lead to a breach of luggage protection. In theory, this backdoor was for TSA agents to use, however, it has failed and proven that security with backdoor is not security at all.
NSA backdoor exploit: A Moscow based security firm Kaspersky discovered a group of hackers who infected computers in 42 countries, out of which Pakistan, India, Russia, Iran and Afghanistan were most infected. Their virus – a self-spreading computer worm called Fanny – has many similarities to the NSA-led Stuxnet virus.
Security Backdoors in Pakistan
As internet penetration increases in Pakistan, the risks from security backdoors are also heightening. Users are not aware of the vulnerability of the personal data they put up on the internet.
Ironically, PTA has reportedly ordered the shutdown of Blackberry’s encrypted communication services for ‘security reasons’. Blackberry uses strong encryption as part of its appeal to its users, which prevents intelligence agencies from intercepting messages. The Blackberry Enterprise Server (BES) doesn’t allow a backdoor for Pakistani security agency to decrypt communications. According to a PTA spokesperson, PTA has issued directions to local mobile phone operators to close BlackBerry Enterprise Services from November 30th.
The fact remains that security backdoors in Pakistan can be exploited by whistleblowers both in Pakistan and by external hackers. They increase vulnerability because while encryption enables criminals to evade law enforcement and blinds the law-enforcing agencies, security backdoors may just end up creating the problems they claim to solve.