Bykea suffered a significant data breach which affected its extensive user database, according to a report published by Safety Detectives.
The Safety Detectives cybersecurity team discovered the elastic server vulnerability during routine IP-address checks on specific ports.
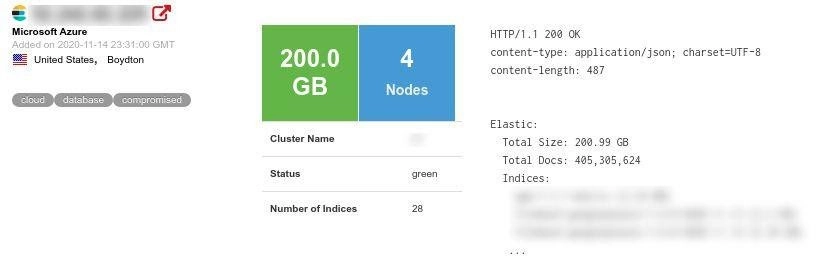
In this instance, Safety Detective’s team discovered that Karachi-based Bykea had exposed all its production server information and allowed access to over 200GB of data containing more than 400 million records showing people’s full names, locations, and other personal information that could potentially be harnessed by hackers to cause financial and reputational damage.
The Elastic instance was left publicly exposed without password protection or encryption which meant that anyone in possession of the server’s IP-address could access the database and potentially remove data from it, added the report.
“It appeared that in September 2020, Bykea suffered a separate breach, during which unidentified hackers reportedly deleted the company’s entire customer database. At the time, Bykea said it was unaffected by the intrusion because it kept regular backups,” it added.
In response, Bykea’s CEO Muneeb Maayr described the cyberattack as “nothing out of the ordinary” given that Bykea is a mobility-based tech firm. It remains unclear whether this latest breach is related to the hack attack in September.
What Was Leaked?
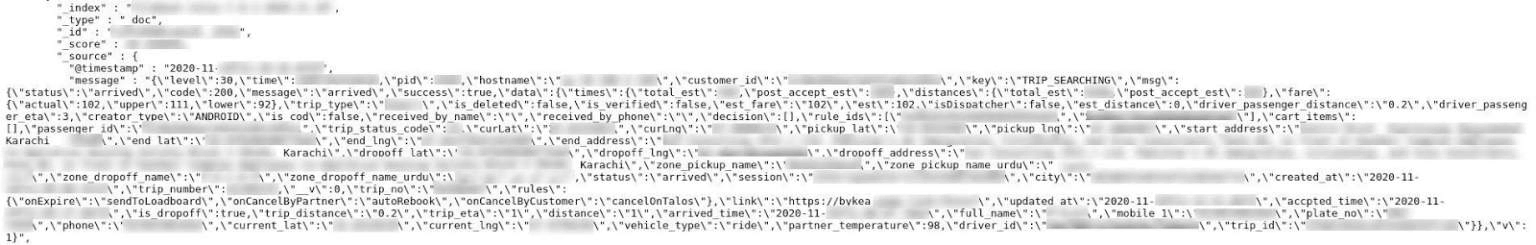
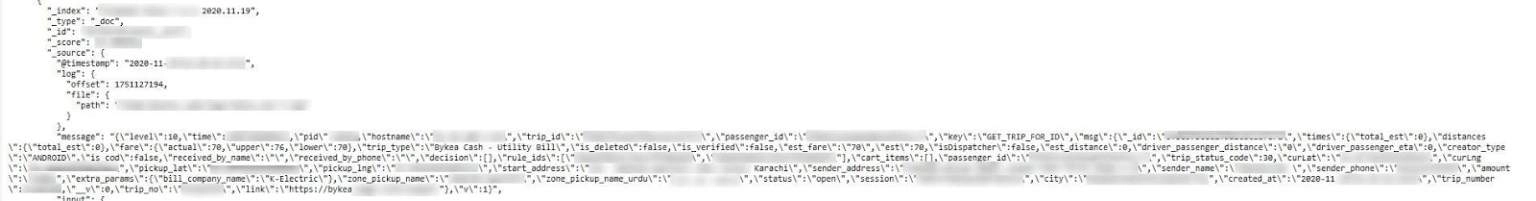
The exposed server contained API logs for both, the company’s web and mobile sites and all production server information. The 200GB database containing 400 million records was regularly updated with internal logs including user details, reported Safety Detectives.
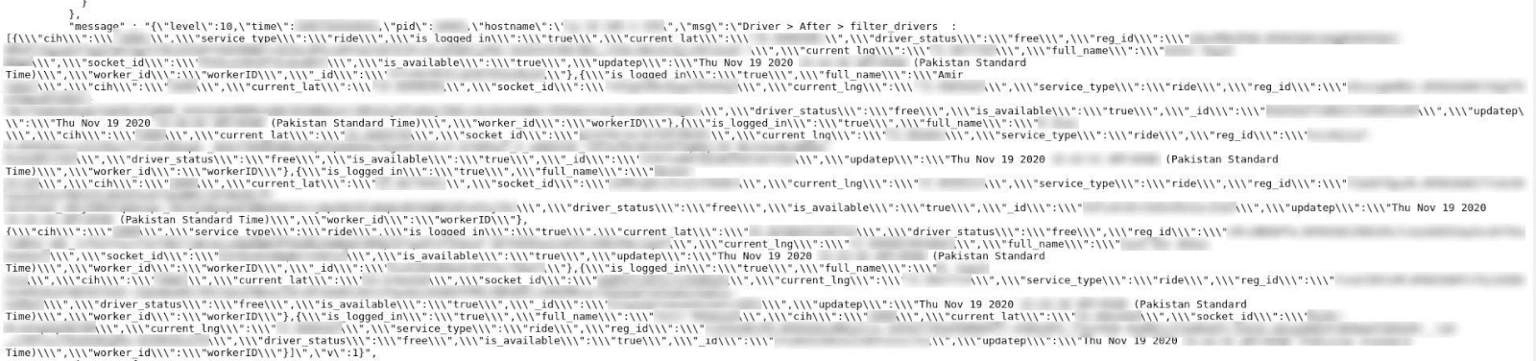
More specifically, the server contained personally identifiable information (PII) for both customers and contracted employees – their drivers, called “partners”, by Bykea.
Bykea Customer’s PII:
- Full names
- Phone numbers
- Email addresses
Bykea Partners’ (drivers’) PII:
- Full names
- Phone numbers
- Address
- CNIC (Computerised National Identity Card)
- Driver license numbers, issuing city and expiry dates
- Body temperature
Other Information Also Left Unsecured:
- Internal API logs
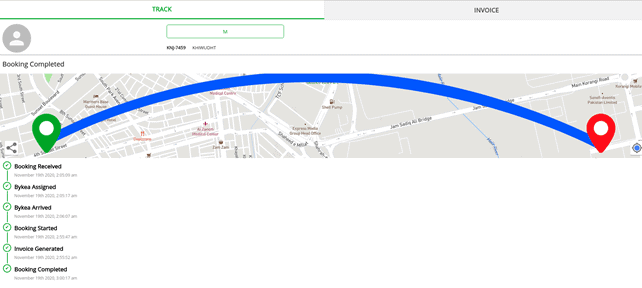
- Collection and delivery location information
- User token ID with cookie details and session logs
- Specific GPS coordinates
- Vehicle information including model and number plate
- Driver license expiry information
- Miscellaneous user device information
- Encrypted IMEI numbers
Safety Detective’s team discovered that Bykea’s server contained customer invoices showing full trip information including where customers were picked and dropped off, driver arrival times, trip distances, fare details and more.
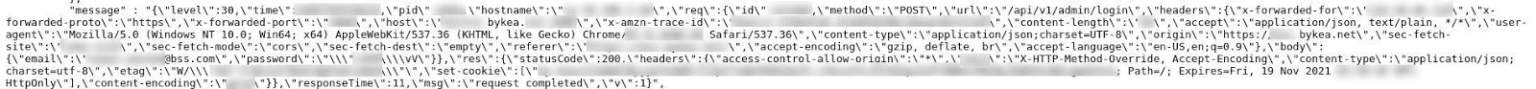
Their team also found Bykea’s internal employee login and unencrypted password information on the unsecured server.
The report further added that Bykea had existing commercial relationships with other Pakistani companies including K-Electric, EasyPaisa and JazzCash allowing customers to pay their electricity bills, get cash and send money with the assistance of a Bykea driver and its app. This data was also stored on Bykea’s database and exposed in the leak.
| Number of records leaked: | 400+ million |
| Number of affected users: | Unknown |
| Size of data breach: | 200+ gigabytes |
| Server location: | Boydton, United States |
| Company location: | Karachi, Pakistan |
It also discovered Bykea’s vulnerability on 14 November 2020. Upon contacting the company on 24 November, Bykea responded immediately by securing its database within 24 hours.
Bykea’s Response
In response to this report, Bykea has issued an official statement.
“Safety Detectives is a team of online security experts and as ethical hackers reported a vulnerability on one of Bykea’s backup logging nodes in November 2020. The company had attracted interest after a public hacking incident on Aug 31st when Bykea’s database was deleted and it took 24 hours to recover a downtime.
Representatives from Bykea were in touch with Safety Detectives who then helped the security team at Bykea solve the vulnerability. Unlike what bloggers in the aftermath of the article on Security Detectives’ site inferred, this was a vulnerability identification, not a breach of stolen data for criminal purposes. The citation of 400 million files mostly comprises millions of GPS pinpoints that Bykea solicits in tracking over a two-week period in 2020 and drivers can be rest assured that national ID data is encrypted now on Bykea.
Bykea has been on a hiring spree since the middle of 2020, bolstering the engineering team as well as specifically adding dedicated security resources to recognize the importance of this function.
Information security is a crucial function and protecting consumer information is a key activity in building trust for rapidly growing digital companies like Bykea” said Muneeb Maayr who went on to say: “Security researchers and teams like Safety Detectives play a crucial role in creating awareness and helping companies all around the world identify and plug their weaknesses, a contribution Bykea explicitly welcomes.
Bykea had engaged a multitude of security companies including SecurityWall that ran pen tests on Bykea’s infrastructure and a vulnerability disclosure program with HackerOne.
The company is exploring ways to build ongoing collaborations with ethical hackers to advance their mutual interests of building a secure digital economy protecting personal information while empowering consumers with new services and digitally enabled value propositions.”

















what else is new?
It is responsibility of these companies to ensure they take all necessary safeguards available to protect sensitive data from being stolen. The govt. needs to ensure firms collecting such data follow all necessary security requirement. Govt. should formulate a body to regulate the cyber security and set minimum requirements and conduct audits. Firms who fail to fulfil these requirements should have the permission to collect sensitive data revoked. The body should also conduct audit of Bykea, and if found that Bikea didn’t take their cyber security seriously, they should be punished adequately.
SO AB HUM DAR JAYE ? AB BOYCCCOT KARE YA CAREEM UBER PE SHIRFT HO JAYE
HUM PAKISTANI KARE TO KIYA KAREN PHIR
Does Bykea have any data? Who use this service?