The Technical University of Berlin has found a way to jailbreak the AMD-based infotainment systems in all modern Tesla cars and run any software.
The hackers can also extract Tesla’s unique hardware-bound RSA key for car authentication in its service network and use voltage glitching to activate software-locked premium features like seat heating and “Acceleration Boost” that Tesla car owners normally have to pay for.
The German researchers told a tech-based media outlet about the breach. The details will also be presented at an international hacker competition on August 9, 2023, under the title ‘Jailbreaking an Electric Vehicle in 2023 or What It Means to Hotwire Tesla’s x86-Based Seat Heater.’
The researchers used AMD research to hack the infotainment system using fault injection attacks to steal knowledge. Tesla’s infotainment system uses an AMD Zen 1 CPU vulnerable to these attacks, thus researchers might leverage previously identified holes to jailbreak it.
The official document states:
For this, we are using a known voltage fault injection attack against the AMD Secure Processor (ASP), serving as the root of trust for the system. First, we present how we used low-cost, off-the-self hardware to mount the glitching attack to subvert the ASP’s early boot code. We then show how we reverse-engineered the boot flow to gain a root shell on their recovery and production Linux distribution.
Potentially Dangerous
The researchers were able to make arbitrary changes that survived infotainment system reboots and Tesla’s ‘over-the-air’ updates by getting root rights.
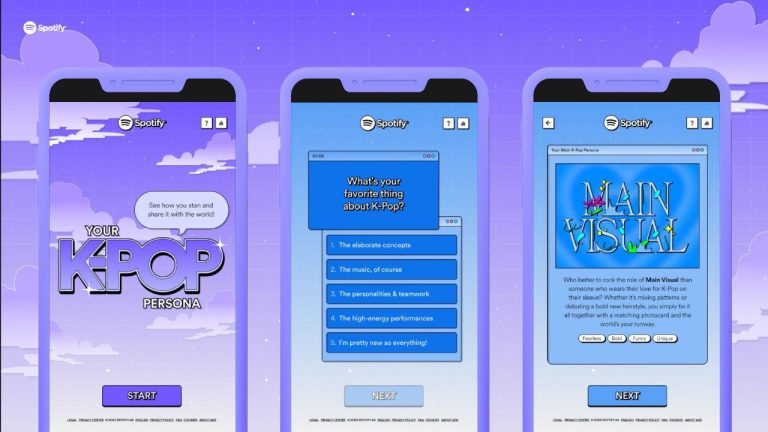
This can also allow you to access and decode the car’s owner’s personal data, phonebook, calendar entries, call logs, Spotify and Gmail session cookies, Wi-Fi passwords, and places visited, which could be dangerous.
The researchers confirmed that their breach could not control the car’s self-driving capabilities. Regardless, the news is likely to send Tesla into panic mode, as the penetration of their car’s system is a huge red flag for the company and the customers.